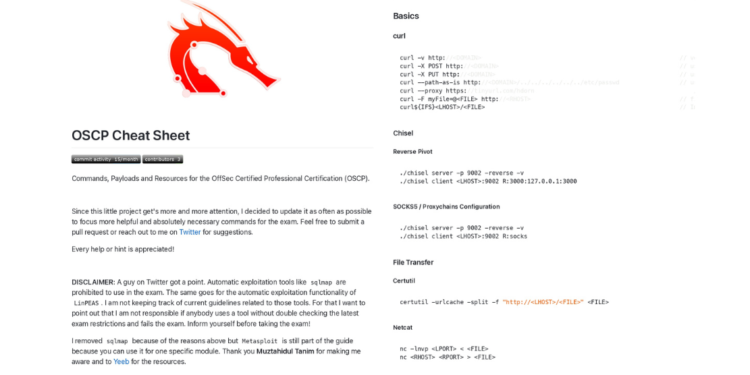
OSCP Cheat Sheet PDF: Your Ultimate 122-Page Ethical Hacking Toolkit
The Offensive Security Certified Professional (OSCP) certification isn’t just a credential—it’s a rite of passage for ethical hackers. Penetration testing demands creativity, precision, and relentless preparation. Whether you’re a novice or a seasoned pro, the OSCP Cheat Sheet PDF is your tactical companion, condensing critical tools, techniques, and workflows into 122 pages of actionable insights.
Why This Cheat Sheet?
- All-in-One Resource: Covers every phase of penetration testing—from recon to post-exploitation.
- Expert-Backed: Crafted by OSCP-certified professionals who’ve survived the labs.
- Time-Saver: Skip the endless Googling; find commands, scripts, and methodologies in seconds.












What’s Inside?
The 122-page OSCP Cheat Sheet PDF is structured into 7 core sections, each targeting a critical skill:
Basics
- curl
- Chisel
- File Transfer
- FTP
- Kerberos
- Ligolo-ng
- Linux
- Microsoft Windows
- PHP Webserver
- Ping
- Python Webserver
- RDP
- showmount
- smbclient
- socat
- SSH
- Time and Date
- Tmux
- Upgrading Shells
- VirtualBox
- virtualenv
Information Gathering
- memcached
- NetBIOS
- Nmap
- Port Scanning
- snmpwalk
Vulnerability Analysis
- Nikto
- Sparta
Web Application Analysis
- Burp Suite
- cadaver
- Cross-Site Scripting (XSS)
- ffuf
- Gobuster
- GitTools
- Local File Inclusion (LFI)
- PDF PHP Inclusion
- PHP Upload Filter Bypasses
- PHP Filter Chain Generator
- PHP Generic Gadget Chains (PHPGGC)
- Server-Side Request Forgery (SSRF)
- Server-Side Template Injection (SSTI)
- Upload Vulnerabilities
- wfuzz
- WPScan
- XML External Entity (XXE)
Database Analysis
- MongoDB
- MSSQL
- MySQL
- NoSQL Injection
- PostgreSQL
- Redis
- sqlcmd
- SQL Injection
- SQL Truncation Attack
- sqlite3
- sqsh
Password Attacks
- CrackMapExec
- fcrack
- hashcat
- Hydra
- John
- Kerbrute
- LaZagne
- mimikatz
- pypykatz
Exploitation Tools
- ImageTragick
- MSL / Polyglot Attack
- Metasploit
Post Exploitation
- Active Directory Certificate Services (AD CS)
- ADCSTemplate
- BloodHound
- BloodHound Python
- bloodyAD
- Certify
- Certipy
- enum4linux-ng
- Evil-WinRM
- Impacket
- JAWS
- Kerberos
- ldapsearch
- PassTheCert
- PKINITtools
- powercat
- Powermad
- PowerShell
- pwncat
- rpcclient
- Rubeus
- RunasCs
- smbpasswd
- winexe
CVEs
- CVE-2014-6271: Shellshock RCE PoC
- CVE-2016-1531: exim LPE
- CVE-2019-14287: Sudo Bypass
- CVE-2020-1472: ZeroLogon PE
- CVE-2021-3156: Sudo / sudoedit LPE
- CVE-2021-44228: Log4Shell RCE
- CVE-2022-0847: Dirty Pipe LPE
- CVE-2022-22963: Spring4Shell RCE
- CVE-2022-30190: MS-MSDT Follina RCE
- CVE-2022-31214: Firejail LPE
- CVE-2023-21746: Windows NTLM EoP LocalPotato LPE
- CVE-2023-22809: Sudo Bypass
- CVE-2023-23397: Microsoft Outlook PE
- CVE-2023-32629, CVE-2023-2640: GameOverlay Ubuntu Kernel Exploit LPE
- CVE-2023-4911: Looney Tunables LPE
Payloads
- Donut
- Exiftool
- GhostScript
- nishang
- Reverse Shells
- ScareCrow
- Shikata Ga Nai
- Web Shells
- ysoserial
Templates
- ASPX Web Shell
- Bad YAML
- Exploit Skeleton Python Script
- JSON POST Request
- Python Pickle RCE
- Python Redirect for SSRF
- Python Web Request
- XML External Entity (XXE)
Who Needs This?
- OSCP Aspirants: Tackle labs and exams with confidence.
- PenTesters: Keep this guide open during engagements for quick reference.
- Cybersecurity Enthusiasts: Learn ethical hacking techniques hands-on.
Why 122 Pages?
This isn’t a skimpy summary—it’s a deep dive designed for real-world application:
- Step-by-Step Walkthroughs: Example: How to exploit a vulnerable SMB service.
- Command Cheatsheets: Ready-to-run code snippets for Kali Linux tools.
- Visual Guides: Network diagrams, flowcharts for attack chains, and report outlines.
Download Your Free OSCP Cheat Sheet
Stop struggling with fragmented notes. Grab your PDF and hack smarter:
🔗 Download the OSCP Cheat Sheet Now