Introduction
As cybersecurity threats continue to evolve, so does the need for qualified professionals. The CISSP (Certified Information Systems Security Professional) is a globally recognized certification that validates your skills and knowledge in information security. This blog post introduces our comprehensive CISSP exam preparation PDF, designed to help you succeed.
Overview About the Document
This CISSP exam preparation PDF serves as an essential tool for anyone looking to enhance their understanding of cybersecurity principles and practices. It combines theoretical knowledge with practical examples to ensure that candidates grasp the complexities of the exam topics.
The Content
The document covers all eight domains of the CISSP Common Body of Knowledge (CBK). Each section includes key concepts, terminology, and real-world scenarios. Additionally, it features practice questions that mirror those found on the actual exam, making your study sessions more effective.
Here’s your cleaned Table of Contents, with all dots and page numbers removed and formatted clearly:
Table of Contents
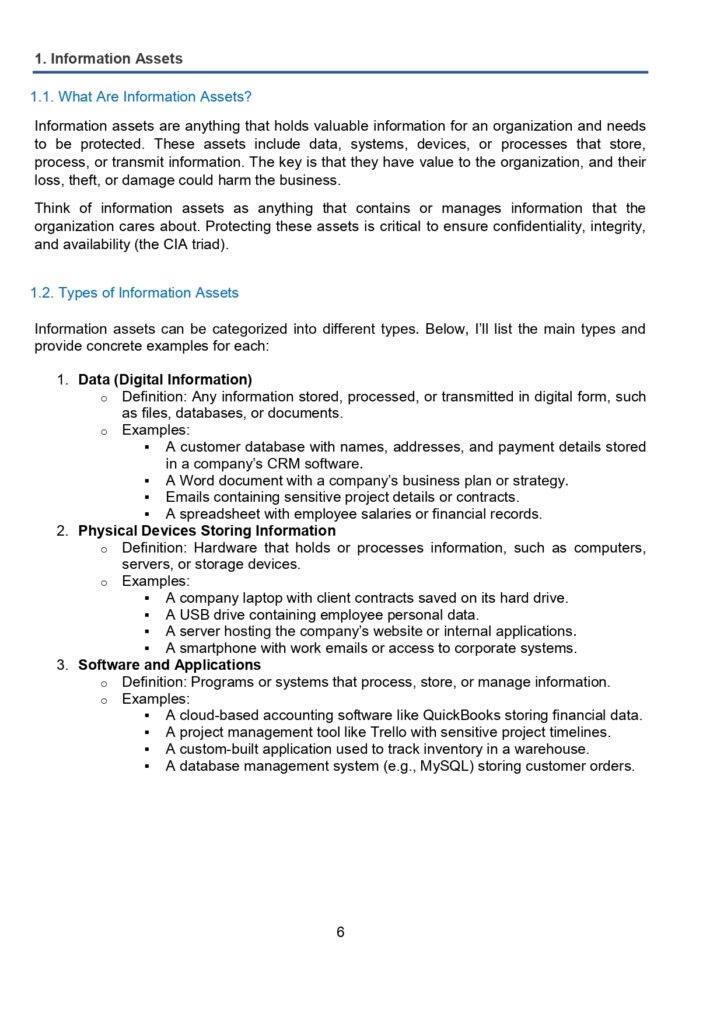
Information Assets
1.1 What Are Information Assets
1.2 Types of Information Assets
1.3 How to Protect Information AssetsInformation Asset Policy
2.1 What is an Information Asset Policy
2.2 Key Characteristics of PoliciesHow to Identify Information Assets
The Asset Owner
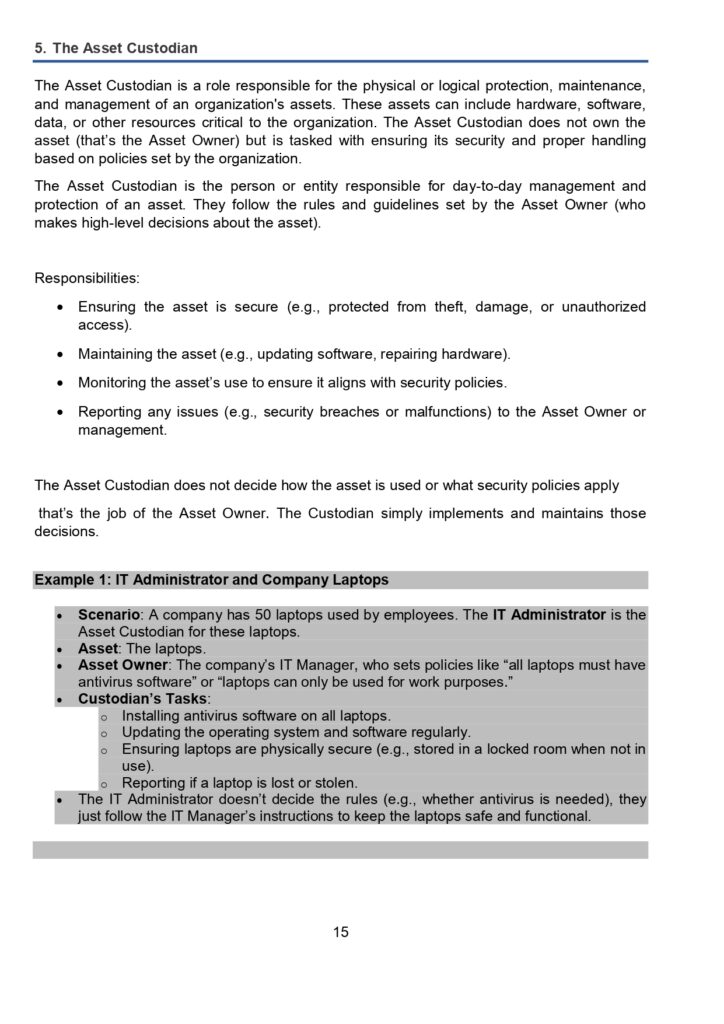
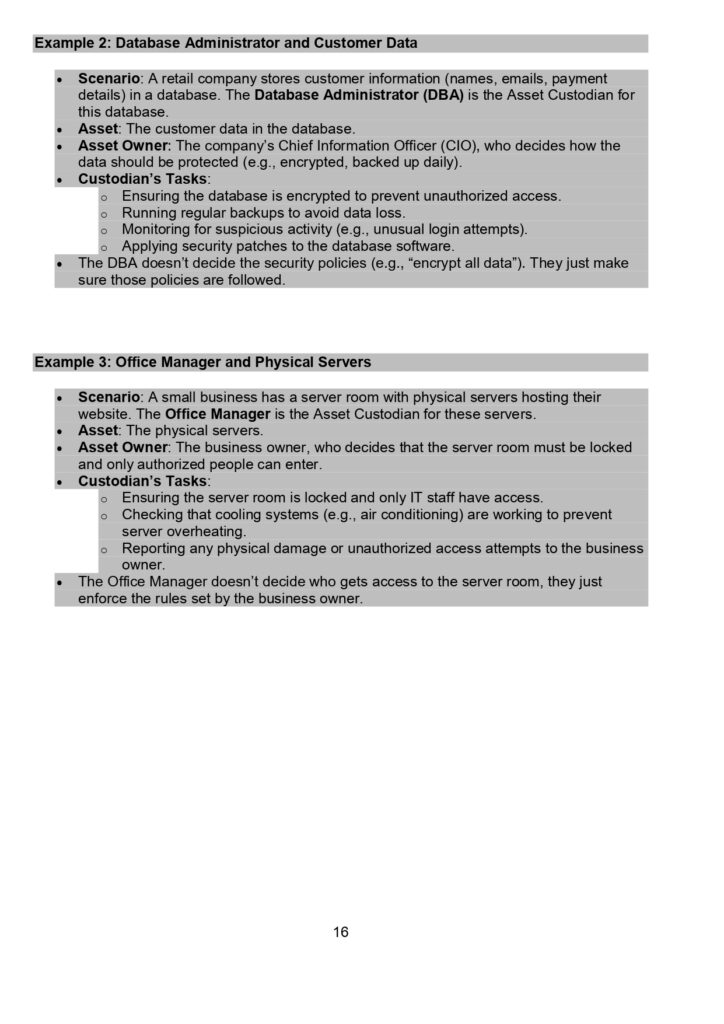
The Asset Custodian
Information Asset Register
Asset Classification
7.1 Classification Policy
7.2 Why is Asset Classification Important
7.3 Steps of Asset Classification
7.4 Military Classification Schemes
7.5 Commercial Classification SchemesData Loss Prevention
Information Asset Management
9.1 Identifying Assets
9.2 Protecting Assets
9.3 Asset Management LifecycleType of Information Assets
10.1 Primary Assets
10.2 Supporting AssetsData Security Control
11.1 Data at Rest
11.2 Data in TransitInformation Security and Asset Protection
12.1 Role-Based Access Control (RBAC)
12.2 Palm Vein Scanner
12.3 Corrective Control
12.4 Detective Control
12.5 Identification
12.6 Technical Control
12.7 LDAP
12.8 SSO System
12.9 Hash
12.10 Dictionary Attack
12.11 Kerberos
12.12 Asymmetric Keys
12.13 Mandatory Access Control (MAC)
12.14 Need to Know
12.15 Discretionary Access Control (DAC)
12.16 TACACS
12.17 Physical Access
12.18 Deterrent Control
12.19 Recovery Control
12.20 Intrusion Detection System
12.21 Least Privilege
12.22 Brute-Force Attacks
12.23 Tempest Equipment
12.24 Promiscuous
12.25 Honeypot
12.26 Man-in-the-Middle (MITM) Attack
12.27 Replay Attack
12.28 Chief Privacy Officer
12.29 Security Administrator
12.30 Mobile Device Management (MDM) Policy
12.31 Data Steward
12.32 Data Processor
12.33 WPA
12.34 Configuration Management Database (CMDB)
12.35 Cloud Access Security Broker (CASB)
12.36 Digital Rights Management (DRM)
12.37 OECD Principle
12.38 Clean Desk Policy
12.39 Thermal Relocking
12.40 NIST SP 800-88
Why the Document
This PDF is invaluable for several reasons. Firstly, it’s conveniently structured to allow for focused study sessions. Secondly, it empowers candidates with the necessary tools to assess their knowledge and identify areas that need improvement. Lastly, the document is regularly updated to reflect the latest CISSP exam trends and criteria, ensuring that you’re studying the most relevant material.
Conclusion
Preparing for the CISSP exam can be overwhelming, but with the right resources, it becomes manageable. Our CISSP exam preparation PDF has been created to simplify your study journey and boost your confidence. Remember, achieving CISSP certification is not just about passing an exam; it’s about gaining the knowledge to protect information systems effectively.
Download from Below Link
Ready to start your journey towards CISSP certification? Download the CISSP exam preparation PDF by clicking Here and take a significant step toward your professional growth.