Master Cybersecurity with Expert-Recommended Tools and Best Practices
Introduction to Penetration Testing
Penetration testing simulates cyberattacks to identify vulnerabilities, ensuring robust defenses. This guide explores the top 25 tools used by professionals, categorized by functionality, with actionable insights for ethical hacking.
Tool Selection Criteria
- Functionality: Aligns with testing phases (reconnaissance, scanning, exploitation).
- Ease of Use: Intuitive for beginners, customizable for experts.
- Community Support: Active updates and documentation.
- Compatibility: Works across OS platforms (Windows, Linux, macOS).
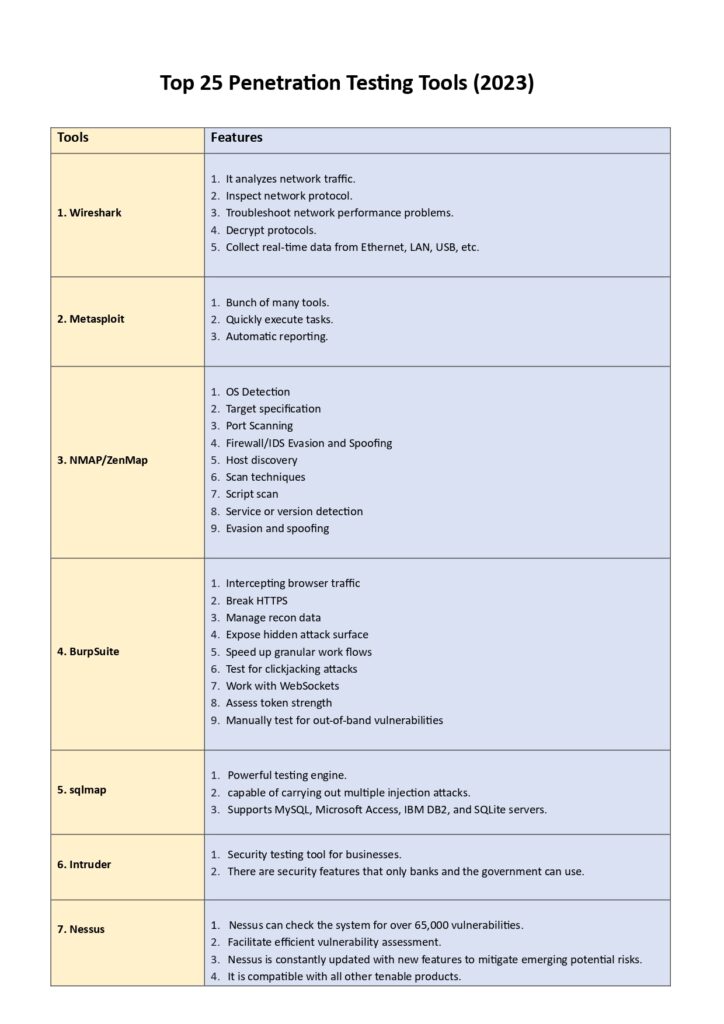
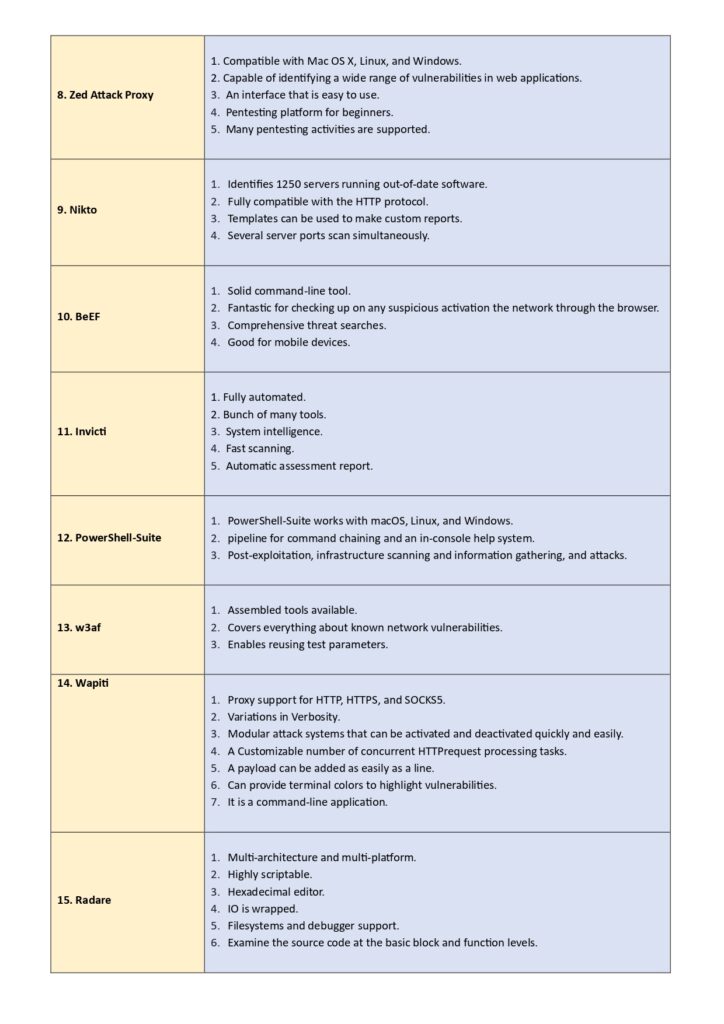
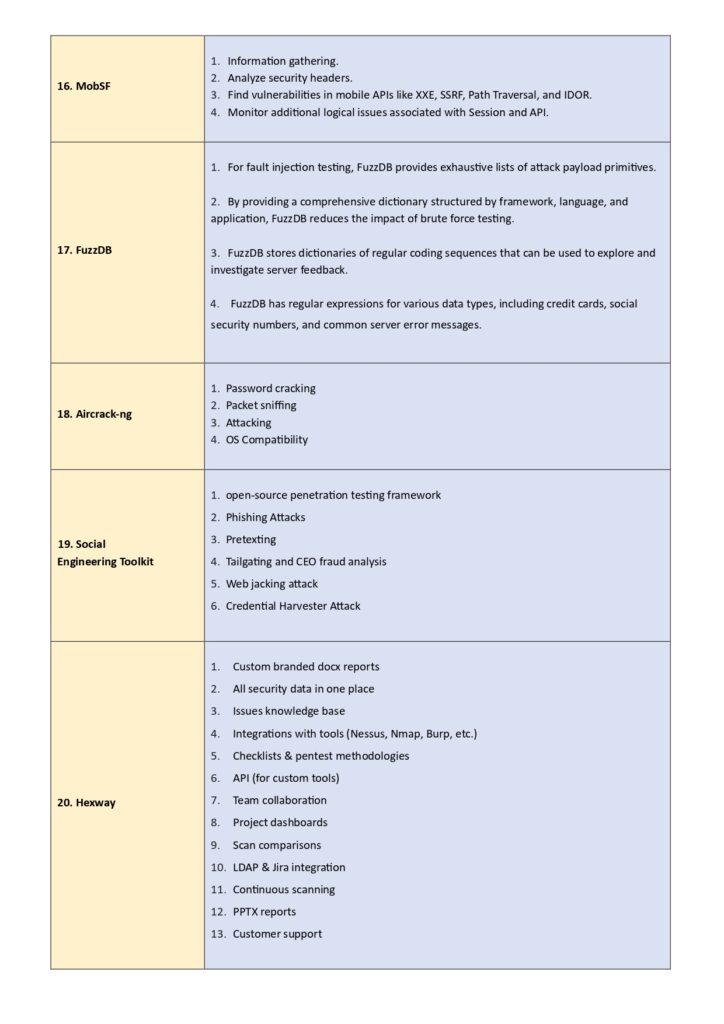
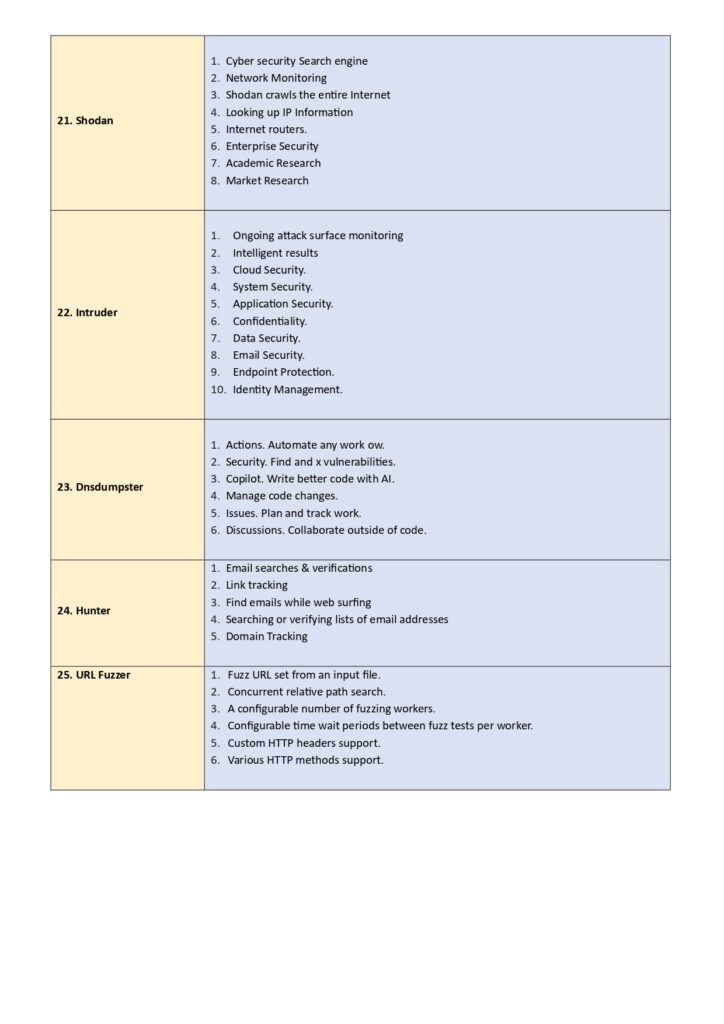
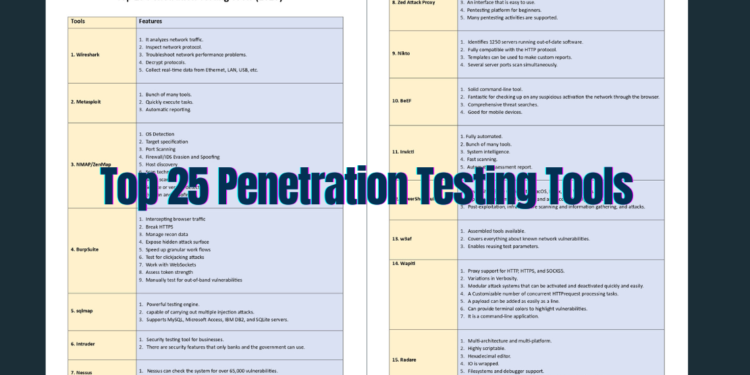
Top 25 Penetration Testing Tools
1. Network Scanning & Enumeration
- Nmap
- Description: Discovers hosts, services, and open ports.
- Features: OS detection, scriptable scans.
- Example:
nmap -sV 192.168.1.1 - Pros: Highly customizable.
- Cons: Steep learning curve.
- Nessus
- Description: Vulnerability scanner for networks and applications.
- Features: Compliance checks, malware detection.
2. Web Application Testing
- Burp Suite
- Description: Intercepts and manipulates web traffic.
- Features: SQLi/XSS testing (Pro version).
- OWASP ZAP
- Description: Open-source web app scanner.
- Features: Automated scanners, API testing.
3. Wireless Network Testing
- Aircrack-ng
- Description: Cracks Wi-Fi encryption (WEP/WPA).
- Use Case: Assessing wireless security.
4. Password Cracking
- John the Ripper
- Description: Brute-force and dictionary attacks.
- Example:
john --wordlist=passwords.txt hashfile
- Hashcat
- Description: GPU-accelerated password recovery.
5. Exploitation Frameworks
- Metasploit
- Description: Develops and executes exploits.
- Command:
msfconsole
- Cobalt Strike
- Description: Post-exploitation and red teaming.
6. Reconnaissance
- Maltego
- Description: Maps relationships between entities (IPs, domains).
- Recon-ng
- Description: Web reconnaissance framework.
7. Vulnerability Scanners
- OpenVAS
- Description: Open-source vulnerability management.
- Nikto
- Description: Web server scanner.
8. Social Engineering
- Social-Engineer Toolkit (SET)
- Description: Phishing and credential harvesting.
9. Post-Exploitation
- Empire
- Description: PowerShell-based post-exploitation.
Best Practices
- Authorization: Always obtain written consent.
- Documentation: Record findings with tools like Dradis.
- Prioritization: Rank vulnerabilities using CVSS scores.
- Reporting: Use templates for clarity (e.g., Executive Summary, Technical Details).
Legal & Ethical Considerations
- Compliance: Adhere to GDPR, HIPAA, and local laws.
- Certifications: Pursue OSCP, CEH, or eJPT for credibility.
Conclusion
Equip yourself with these tools to identify and mitigate risks effectively. Pair this guide with labs on TryHackMe or Hack The Box for hands-on practice.
Download PDF
Key Features of the PDF:
- Command Cheatsheets: Quick references for Nmap, Metasploit, and more.
- Tool Comparison Tables: Features, pricing, and use cases.
- Sample Report Template: Streamline stakeholder communication.
Stay Secure, Stay Proactive. 🔒
Share this guide to empower your team and build a safer digital world.